The landscape of network security is evolving rapidly, with enterprises increasingly adopting hybrid cloud environments. As these environments grow in complexity, so too does the challenge of managing network security policies effectively. Misconfigurations, compliance gaps, and vulnerabilities can expose organizations to significant risks. To tackle these challenges, Network Security Policy Management (NSPM) offers a comprehensive solution.
The Complexity of Hybrid Cloud Environments
Hybrid cloud environments, which integrate on-premises systems with public and private cloud services, offer greater scalability and flexibility. However, this integration introduces unique configurations and potential vulnerabilities. Every segment of a hybrid cloud has its own set of security requirements, complicating the task of maintaining a cohesive security posture. As organizations strive to capitalize on the dynamic nature of hybrid clouds, the complexity in managing these varied and interconnected systems presents challenges that must be addressed efficiently.
The Risks of Misconfigurations
One of the most significant risks in hybrid cloud environments is misconfigured security policies. Gartner has found that around 99% of firewall breaches are due to misconfigurations rather than flaws in the technology itself. This statistic underscores the critical importance of ensuring that security policies are consistently and correctly applied across all segments of the network. Misconfigurations can lead to unauthorized access, data breaches, and severe regulatory penalties, exposing organizations to numerous threats.
Effective NSPM tools can help identify and rectify these misconfigurations by providing a detailed overview of security policies and their implementations. Regular audits, combined with an automated approach to monitoring and validating policy configurations, can significantly mitigate the risks associated with manual errors. Moreover, leveraging advanced analytics and machine learning algorithms, NSPM can proactively flag potential misconfigurations before they lead to security breaches, ensuring a robust and resilient security framework.
Compliance Challenges
Compliance with regulations such as GDPR, PCI DSS, and HIPAA is another critical aspect of managing hybrid cloud environments. These regulations demand stringent controls and continuous monitoring to protect sensitive data. The challenge lies in the complex and dynamic nature of hybrid clouds, which often span multiple jurisdictions and regulatory frameworks. Adhering to these diverse standards requires continuous adjustments to security policies and the ability to demonstrate compliance through detailed reporting and audits.
NSPM tools facilitate compliance by automating many of the processes involved in monitoring and reporting. This continuous monitoring ensures that security policies remain aligned with regulatory requirements, while automated reporting provides the necessary documentation for audits and compliance checks. Additionally, NSPM systems can integrate with other compliance tools to streamline workflows and ensure a holistic approach to regulatory adherence. By incorporating continuous compliance checks into the security management framework, organizations can minimize the risk of non-compliance, avoid financial penalties, and build trust with stakeholders.
Centralized Visibility
Centralized visibility is a cornerstone of effective NSPM, providing an overarching, unified view of an organization’s security posture. By consolidating security policy data into a single platform, organizations can achieve real-time, comprehensive visibility across all segments of their hybrid cloud environment. This approach eliminates blind spots and ensures prompt identification and addressing of all vulnerabilities, enhancing the overall security framework.
Single Dashboard Advantage
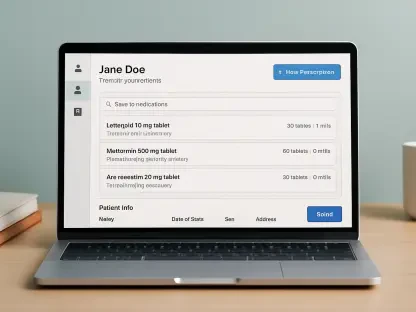
A centralized dashboard offering a single view into an organization’s entire network security posture provides significant advantages. This unified visibility enables security teams to detect and respond to potential threats more swiftly and effectively, leveraging consolidated information to improve response times. With all relevant data and metrics available at a glance, teams can make informed decisions, prioritize critical issues, and coordinate their efforts more efficiently.
Moreover, a single dashboard can streamline the management of security policies across different environments, reducing administrative overhead and simplifying compliance tracking. It allows for seamless integration of various tools and data sources, presenting a holistic view of the security landscape without the need to switch between multiple interfaces. This integration not only improves operational efficiency but also enhances the ability to maintain a consistent and comprehensive security posture.
Eliminating Blind Spots
Consolidating disparate data into a unified view helps eliminate blind spots, which are often the entry points for breaches. Blind spots occur when security policies or monitoring tools fail to account for certain aspects of the network, potentially leaving vulnerabilities unaddressed. By leveraging a centralized platform, organizations can ensure that no segment of their hybrid cloud environment goes unmonitored.
The use of advanced analytics and visualization tools within NSPM systems can further enhance visibility, enabling security teams to identify and address anomalies and potential threats more proactively. These tools can provide insights into traffic patterns, detect unusual behavior, and highlight areas that require further investigation. By eliminating blind spots, organizations can improve their detection and response capabilities, reducing the risk of successful attacks and minimizing the potential impact of security incidents.
Automating Policy Management
Automating policy management is another critical aspect of NSPM, reducing the reliance on manual processes that are prone to human error. By automating tasks like rule analysis, compliance reporting, and real-time monitoring, organizations can enhance accuracy and efficiency, ensuring that policies are consistently and accurately applied across the entire hybrid cloud environment.
Reducing Human Error
Manual policy management processes are not only time-consuming but also susceptible to mistakes that can compromise security. Human error, whether due to oversight, lack of knowledge, or simple fatigue, can introduce vulnerabilities and gaps in the security framework. Automating policy management minimizes these risks by ensuring that policies are consistently enforced according to predefined rules and parameters, without manual intervention.
Automation tools can handle routine tasks like policy updates, rule validation, and compliance checks, reducing the likelihood of errors and allowing security teams to focus on more strategic activities. Additionally, automated workflows can provide a clear audit trail, making it easier to trace and address any issues that arise. By leveraging automation, organizations can enhance the reliability and consistency of their security policies, improving their overall security posture.
Enhancing Efficiency
Automation allows security teams to focus on higher-value activities, such as threat analysis and response, rather than mundane and repetitive tasks. This shift enhances operational efficiency and allows organizations to scale their operations effectively. Automated policy management streamlines processes, reduces administrative overhead, and improves the speed and accuracy of policy enforcement.
Furthermore, automation enables real-time monitoring and response, allowing security teams to detect and address potential threats more quickly. Automated systems can continuously analyze network activity, identify anomalies, and trigger alerts or corrective actions as needed. This proactive approach reduces the window of opportunity for attackers and helps prevent security incidents before they can cause significant damage. By enhancing efficiency through automation, organizations can better manage the complexities of hybrid cloud environments and maintain a robust security posture.
Proactive Risk Mitigation
NSPM aims to be proactive rather than reactive, focusing on identifying vulnerabilities and compliance gaps before they can be exploited. By leveraging continuous monitoring and automated tools, organizations can address issues before they escalate into significant breaches, maintaining a robust security stance.
Continuous Monitoring
Continuous monitoring and reporting are essential to ensure that even the most complex environments meet industry standards. This proactive approach helps in addressing issues before they escalate into significant breaches. Continuous monitoring involves real-time analysis of network activity, identifying potential threats, and triggering appropriate responses to mitigate risks.
Advanced NSPM tools can provide continuous monitoring across all segments of a hybrid cloud environment, ensuring that policies remain aligned with security requirements and regulatory standards. These tools can detect deviations from expected behavior, identify emerging threats, and initiate automated responses to contain and remediate issues. Continuous monitoring not only enhances security but also provides valuable insights into the overall health and performance of the network, enabling organizations to make informed decisions and optimize their security strategies.
Identifying Vulnerabilities Early
Early identification of vulnerabilities allows for timely remediation, preventing potential threats from materializing into actual breaches. By leveraging NSPM, organizations can implement security measures before threats become critical, maintaining a robust security stance. NSPM tools can analyze network traffic, detect anomalies, and identify patterns that may indicate potential vulnerabilities or targeted attacks.
This proactive approach allows organizations to address vulnerabilities at their source, implementing corrective actions such as patching, policy adjustments, or additional security measures. Early detection and remediation reduce the risk of successful attacks and minimize the impact of potential breaches. Additionally, NSPM tools can provide detailed reports and analytics, helping organizations understand the root causes of vulnerabilities and improve their overall security posture.
Conclusion: Future of NSPM
The landscape of network security is experiencing rapid evolution, as enterprises increasingly embrace hybrid cloud environments. With the surge in adoption, the complexity of these environments has also risen, making the task of managing network security policies more challenging. Enterprises face risks due to misconfigurations, compliance gaps, and vulnerabilities, which can lead to significant threats. Addressing these challenges requires a robust strategy, and Network Security Policy Management (NSPM) presents a comprehensive solution to mitigate these risks. NSPM streamlines the process of defining, administering, and enforcing security policies across diverse network environments. By employing NSPM, organizations can ensure that their network security policies are consistently applied, reducing the likelihood of errors and maintaining compliance with regulatory standards. In an era where cyber threats are increasingly sophisticated, having an effective NSPM system is crucial for safeguarding sensitive information and maintaining operational integrity.