As a veteran in the intersection of risk management and Insurtech, Simon Glairy has spent years deciphering how small and medium-sized businesses navigate the increasingly turbulent waters of digital threats. With the recent release of data showing a significant shift in SMB sentiment, his perspective is more critical than ever. We are seeing a landscape where cyberattacks are no longer catastrophic anomalies but have instead become a predictable “new normal” for North American firms. This discussion explores the psychological shift among business leaders who have survived multiple breaches, the growing tension between the fear of advanced AI and the mundane reality of phishing, and the emerging role of insurance providers as the primary architects of corporate security standards. By looking at the hard numbers—from the 82% of leaders fearing global conflict to the nearly half of firms operating on flat budgets—we can begin to map out a more resilient path forward for the modern enterprise.
Organizations that have survived multiple cyberattacks often report higher confidence in their resilience than those never targeted. Why does surviving a breach increase a leader’s sense of security, and what metrics should they use to distinguish genuine resilience from a false sense of safety?
There is a fascinating, almost paradoxical psychological shift that occurs when a business is battle-tested. In the United States, 91% of SMBs that have weathered multiple incidents report feeling confident in their resilience, a figure that stays remarkably high at 88% in Canada. This “survivor’s glow” often stems from the fact that they have already faced the worst-case scenario, navigated the panic, and come out the other side with their operations intact. However, a leader must be careful not to mistake the mere absence of total failure for a state of optimal security. True resilience should be measured by the speed of recovery and the stability of the budget; for instance, 45% of frequently targeted US firms now report their cybersecurity funding is “more than sufficient,” suggesting that real safety comes from the financial and structural capacity to absorb a hit rather than just the luck of surviving one.
AI-powered malware is a primary concern for many businesses, yet traditional issues like phishing and unpatched vulnerabilities cause the most actual damage. How can organizations balance the hype of emerging threats with basic security hygiene, and what specific training improvements actually change employee behavior?
It is easy to get caught up in the cinematic fear of AI-powered malware, which tops the worry list for 32% of US and 34% of Canadian businesses, but the “gritty” reality is far more mundane. While leaders lose sleep over futuristic threats, 27% of US incidents are still being triggered by simple phishing, and 25% are caused by unpatched vulnerabilities that have likely been sitting in the system for months. To bridge this gap, we are seeing a massive movement toward structured training programs, with over 90% of SMBs now viewing awareness as a critical investment. The most effective change comes from moving beyond boring annual lectures and into active phishing simulations, a tactic now adopted by 44% of US and 47% of Canadian firms. These simulations create a “muscle memory” for employees, teaching them to feel that slight prick of suspicion when an email looks just a little too perfect, which is a far better defense than any expensive software.
Cyber insurance providers are increasingly mandating technical controls, such as continuous monitoring and managed detection, as conditions for coverage. How does this insurer-driven model shift internal security priorities, and what are the potential risks of relying on a single insurance partner for managed security services?
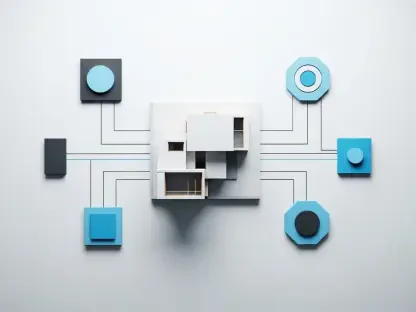
We are witnessing a quiet revolution where insurance companies are becoming the de facto regulators of the SMB world. With 86% of US firms and 78% of Canadian firms now carrying cyber insurance, the policy document is starting to dictate the IT roadmap more than the internal strategy does. In the US, 55% of insured businesses are now required to implement specific technical measures, often involving continuous monitoring or Managed Detection and Response (MDR), just to keep their coverage. The danger here is the creation of a “security monoculture” where everyone is using the same few tools vetted by a handful of insurers. If a single vendor in that ecosystem fails or is compromised, the systemic risk is massive, yet 35% of US firms that outsource are already leaning on their insurers to provide these exact managed services.
Many organizations are concerned about security monocultures where a single vendor provides the entire ecosystem of protection. What are the operational dangers of such a setup during a major outage, and how can a small business effectively diversify its security stack without overcomplicating its management?
The fear of putting all your eggs in one digital basket is very real, with 72% of US businesses and 66% of Canadian firms expressing deep concern over vendor monocultures. When you rely on a single ecosystem for everything—from your firewall to your email filtering—a single point of failure can effectively ghost your entire organization during a major outage. For a small business, the goal isn’t necessarily to buy twenty different products, but to ensure that their critical functions are decentralized enough that one vendor’s downtime doesn’t freeze the entire company. You can start by diversifying the “human” layer and the “technical” layer, perhaps using a traditional MSP for infrastructure while employing a separate, specialized vendor for MDR. This adds a layer of redundancy that protects you from the cascading failures that often haunt large-scale, single-vendor environments.
While cyberattacks are now viewed as a standard business cost, many small businesses expect their security budgets to remain flat this year. How can a leader optimize a stagnant budget against rising risks, and what specific anecdotes illustrate the cost-benefit of investing in training over software?
Optimizing a flat budget requires a cold, hard look at where the leaks are actually happening, especially since 47% of US and 52% of Canadian SMBs don’t expect their spending to change this year. Instead of chasing the latest “AI-ready” firewall, savvy leaders are doubling down on the human element, with 42% of US firms planning to increase their training spend despite stagnant overall budgets. I often think of a firm that avoided a multi-million dollar ransomware hit not because of a million-dollar software suite, but because a junior clerk noticed a slightly off-color logo in a “urgent” invoice email—a skill honed through regular phishing simulations. Investing in training is essentially buying “human software” that updates itself with every simulation, providing a much higher return on investment than a hardware box that will be obsolete in three years.
Most business leaders now associate geopolitical conflicts and cyber warfare with direct risks to their local operations. What practical steps can a firm take to shield its supply chain from global disruptions, and how do you translate these high-level political threats into daily technical tasks?
It is a sobering reality that 82% of SMBs now believe cyber warfare and global conflict pose a direct threat to their bottom line, yet supply chain compromise strangely sits near the bottom of their list of immediate worries. Bridging this gap requires translating “global tension” into “local vigilance” by auditing every third-party connection that has access to your data. Practically, this means moving beyond simple password policies to implementing strict security monitoring, a gap that currently accounts for 27% of incidents in the US and 20% in Canada. Shielding the supply chain isn’t about solving world peace; it’s about ensuring that your vendor’s weak security posture doesn’t become your “back door” for a state-sponsored actor looking for an easy entry point.
What is your forecast for SMB cybersecurity?
I believe we are entering an era where the “insurance-security complex” will become the primary driver of how small businesses operate. We will see a shift where insurance premiums are tied directly to real-time security telemetry, meaning companies that lack continuous monitoring will simply become uninsurable or be forced into extremely expensive, insurer-mandated managed service pools. While the fear of AI will continue to dominate the headlines, the winners will be the organizations that ignore the hype and master the fundamentals of credential hygiene and employee simulations. Ultimately, the 54% of US firms that experienced an incident last year are teaching us that cybersecurity is no longer a project with a finish line, but a continuous, operational rhythm that must be woven into the very fabric of daily business life.